The internet of things (IoT) devices have been around for a number of years now, but very few smart sensors have any decent level of data security. For many organisations the issue of data security and secure remote updates to legacy products has become of paramount importance. Unfortunately, many of the engineers who design sensor products have little or no understanding a security algorithms, leading to systems that can be easily hacked – the fiasco of the UK smart meter system is a good example.
Algorithms to the rescue
Algorithms and mathematics are usually regarded by many organisations as ‘academic black magic’ and are generally overlooked as a solution for a robust IoT commercial application. Nevertheless, some of you may be surprised by how old the concept of algorithms actually are in solving real world problems.
A few weeks ago, I looked through my old PhD thesis and stumbled across a reference to one of world’s first documented algorithms from the 9th century mathematician, Al-Khwarizmi (where, the word ‘algorithm’ is derived from al-Khwarizmi’s name).
Al-Khwarizmi undertook pioneering work in algebra, which was popularized in his book, “al-Mukhtasar fi Hisab al-Jabr wa l-Muqabala” and altered society’s perspective of analyzing problems, be they a simple domestic chore or a complex mathematical concept.
An excerpt from “Al-Mukhtasar fi Hisab al-Jabr wa l-Muqabala” for the solution to x^2 + 10x = 39.
Translation: For the squares and roots equal to a number, it is as saying: a square and ten of its roots is equal to thirty-nine dirhams. The solution is to halve roots, equal to five in this problem, then, multiplying the root by itself then this will be twenty-five. Then add it to thirty-nine and this will be sixty-four. Then take the square root, which will be eight and subtract from it half the root, which is five. The remainder is three and that is the root you are seeking and the square is nine.
I had forgotten (well, it was 14 years ago!) how elegant Al-Khwarizmi work actually was, and how I’m sure he would probably smile at the challenges that we’re facing today. Nevertheless, without his pioneering work, we wouldn’t have any of the IoT and security algorithms that we take for granted today.
Solutions in the 21st century
We’ve been pleasantly surprised by the rich offering from commercial IC vendors, such as: Atmel, NXP and Analog Devices in producing secure micro-controllers for the IoT market. Many of these micro-controllers include all of the necessary hardware encryption building blocks needed for building a secure IoT sensor, and some even offer a decent amount of processor power for data analytics algorithms.
Sounds ideal, right?
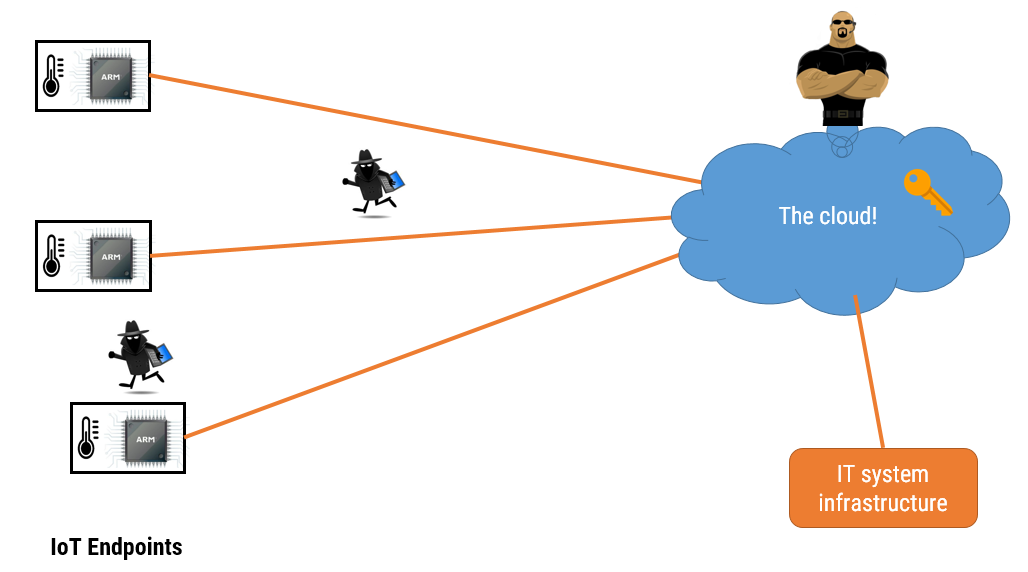
The Achilles heel of all of these solutions is how engineers implement them in a system. The micro-controller itself may be ‘secure’, but what about the system architecture (i.e. the algorithmic building blocks and and how they interact with each other). And what about encryption keys? How are they stored and updated? For the UK smart meter system mentioned above, the system just used one key for the whole system – not very secure ! It is this fact that is painfully overlooked by many, and as such, which eventually leads to the system being hacked and rendered useless.
In short, hardware based encryption technology is a great step in right direction for IoT device security, but without good understanding of encryption technology as part of the system architecture the solution is doomed to failure.