How biomedics can benefit from IoT:
- Improve the quality and effectiveness of your medical treatment with IoT and thus the quality of life for your patient
- Do you want to spend your time on patients who really need it? Treat more patients in a better way in the same time within the same budget
- Improve and fasten your patient’s recovery… with knowledge of results of the treatment of thousands of patients
- Be on the forefront of IoT and help your patients in ways that were not possible before
- Better measurement with clean data
- Security: get control of your patients’ privacy
Sensor devices improve the quality of treatment and thus of life itself. Through prevention, medical treatment itself or therapy. Sensors solutions help to improve life and can even help to save lives. No wonder medical devices are one of the fastest growing sectors in IoT.
Households want to benefit from the newest possibilities IoT devices deliver. For better health and independence as much and as long as possible. Sensor devices can especially help people with chronic diseases, elderly people and people who need constant supervision.
For medical service providers, sensor devices can help to provide the best service as possible in times of increasing medical demand but also on a growing focus on costs. So, budgets must be spent in the best way as possible. Sensors and other IoT devices can help medical facilities to treat more patients in a better way and more efficiently.
How Advanced Solutions helps
Our services can help you in the following ways:
- IoT solutions
- Sensor measurement
- Security
IoT solutions
Our systems prevent accidents from happening and reduce the response time of healthcare professionals.
Sensor measurement
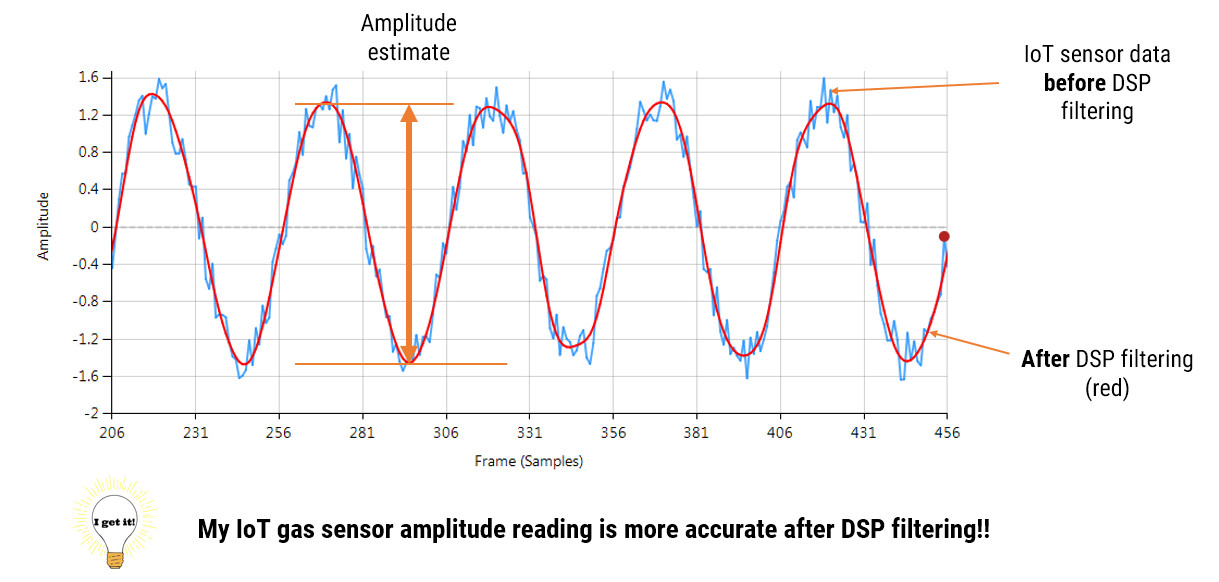
In biomedical applications, sensors are already used in a lot of ways. EMG and ECG are just some examples. For making the right decisions on treatment, the measurement has to be accurate. However, most sensor data suffer from the following problems:
- Powerline interference, measurement noise and glitches
- Baseline wander and offsets from analog instrumentation electronics
- Biomedical sensors are sending weak signals. So, in some cases, those signals have to be strengthened before analysis is possible.
Sometimes the filtering is done in the hardware of the medical equipment. However, these are very costly solutions. And most of the times, a simpler solution and thus less costly solution is what is being sort after.
ASN Consultancy is the modern way of working of algorithm design to separate the wanted sensor signals from the undesirable unwanted signals. So, you can analyse and take action on clean and accurate sensor data.